Companies
Cloudy Picture: password security in post Jennifer Lawrence world

by David Eyes
Founder, Passqi
Say no to passwords in the cloud
The news this week about apparently hundreds of (very) private pictures of celebrities apparently being siphoned from 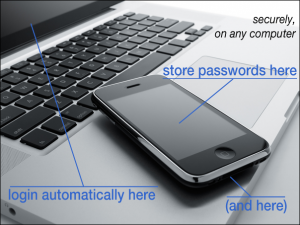 Apple’s iCloud service reminds us again how careful we need to be with what exactly winds up in the cloud.
Apple’s iCloud service reminds us again how careful we need to be with what exactly winds up in the cloud.
One might wonder what the pictures were doing there in the first place: sophisticated email users, certainly in the corporate environment, have long understood that you shouldn’t really say anything in an email that you wouldn’t be comfortable if it were read by others than the intended recipients (like: anyone). Likewise this applies to photographs on the internet – especially for “high value” targets.
While the Apple security team will no doubt be double and triple reviewing their practices and procedures, it appears that this breach was some form of targeted attack using perhaps a combination of brute force techniques, social engineering, and possibly, exploitation of “soft spots” in the iCloud infrastructure.
The cloud offers a fixed-location target for the determined attack
As for email and certain photographs, how much more so for passwords, a “high value” target we call have — encrypted though they may be. We all love the convenience that syncing (and sharing) things through the cloud can give us. However, as detailed in a recent security review of password applications cited by Ars Technica last month, “Severe” password manager attacks steal digital keys and data en masse, solutions which store passwords in the cloud are vulnerable to the same kind of breach as in the Jennifer Lawrence situation. Like services such as iCloud, vendors who host passwords in the cloud present a fixed-location target for the determined attack, and once breached, provide access to everything, all in one place.
Continue reading full article here: https://www.passqi.com/cloudy-picture/
###
Tagged passQi, password security